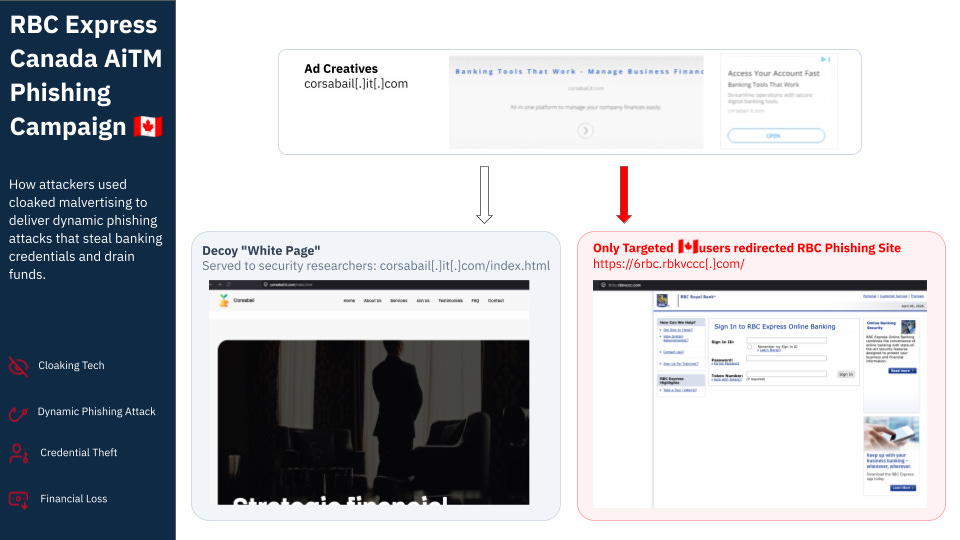
RBC 🇨🇦 Express AiTM Phishing Campaign
How AiTM malvertising bypasses MFA to drain Canadian business banking accounts, leaving victims in a months-long race to recover their stolen assets and identities.
RBC Express Online Banking is the commercial/business banking portal for Royal Bank of Canada.
This phishing campaign is an example of a lower-volume, targeted attack where the payload is a sophisticated automated AiTM relay kit that combines mainstream cybersecurity threats (credential harvesting, multi-factor authentication bypass) with malvertising distribution TTPs (cloaking).
A Quick Primer: Ad Tech And How Malvertisers Exploit It
When you see an ad on a website or mobile app, you probably don’t think about how it got there. Behind every ad is the programmatic ad tech industry: where an advertiser bids on an ad slot, an auction happens in milliseconds, and the winning ad gets served. It’s designed to be targeted, efficient, and scaled—but the system relies on trust.
Here’s a simple example: You engaged with some Easter content online. Ad networks record that interest, and when you check the weather on your phone, an auction runs among advertisers. A retailer selling Easter bunnies bids and wins. The ad gets served and you see bunnies! Most of us never think about the complex machinery behind that moment.
But when a malicious actor bids in that same auction, programmatic ad tech is used to deliver all manner of payloads to victims, deliberately targeted and at scale.
Cloaking in Ads
Cloaking is an evasive technique that detects and routes inbound traffic based on specific conditions, such as user-agent strings, IP geolocation, OS, or even more. Attackers use it to serve benign content “white page” to some traffic (Users not in the attackers scope, bots & crawlers, security companies, Ad tech policy reviewers, etc.) while delivering malicious payloads only to users they want to target. Ad networks ban cloaking because it is deceptive and harmful to users.
In practice, cloaking works something like this: the attacker’s server automatically fingerprints people who engage with the ad campaign. Targeted users are taken to the malicious landing page—either through a redirect or a specific URL hosted on the same site. This is called the “money page”, which contains the payload. In this case, it is the redirect to a separate phishing site branded as RBC Express Online that contains the credential harvester. Scanners and researchers never see the malicious site because they never receive the redirect request. The attack remains active until caught or as long as the attacker funds the ads.
Static Phishing vs. AiTM: Why This Campaign Is More Dangerous
Most phishing attacks work like this: attacker creates a fake login page, victim enters credentials, attacker steals them. If you’re using multi-factor authentication (MFA), the attack stops there—your credentials alone can’t login.
AiTM (Adversary-in-the-Middle) attacks are different. The attacker doesn’t just keep your credentials; instead, they intercept your login attempt in real time and attempt to log in as you on the real bank while you’re still on their fake page. Essentially, when you hand them your password and multi-factor authentication token, they hand that token to the real bank. If the bank accepts it, the attacker gets in and rapidly starts draining your funds or modifying account details.
This campaign implements an automated AiTM relay, and it’s running at scale against an actual bank. Real bank employees are likely to notice a new login session from an odd IP or geography. This attack defeats that detection by relaying the credentials through the victim’s own session.
Attackers will often lock you out of the account by changing your password (since they already have it), recovery info etc. It gives them time to steal money, and they count on the time it takes victims need to first discover the compromise, and call or visit the bank to regain access to their account.
The Malvertising Attack Chain
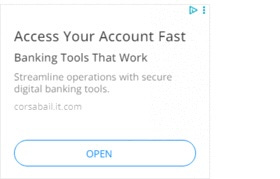
The Ads
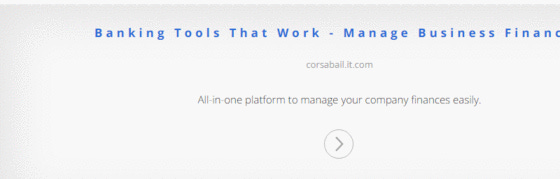
The attacker enters programmatic real-time bidding auctions, targeting Canadian users based on specific criteria. When their bid wins, the ad is served under the advertiser domain corsabail.it.com with creative that appears benign and legitimate (see below). They pass as a generic B2B financial tools—nothing visually suspicious.
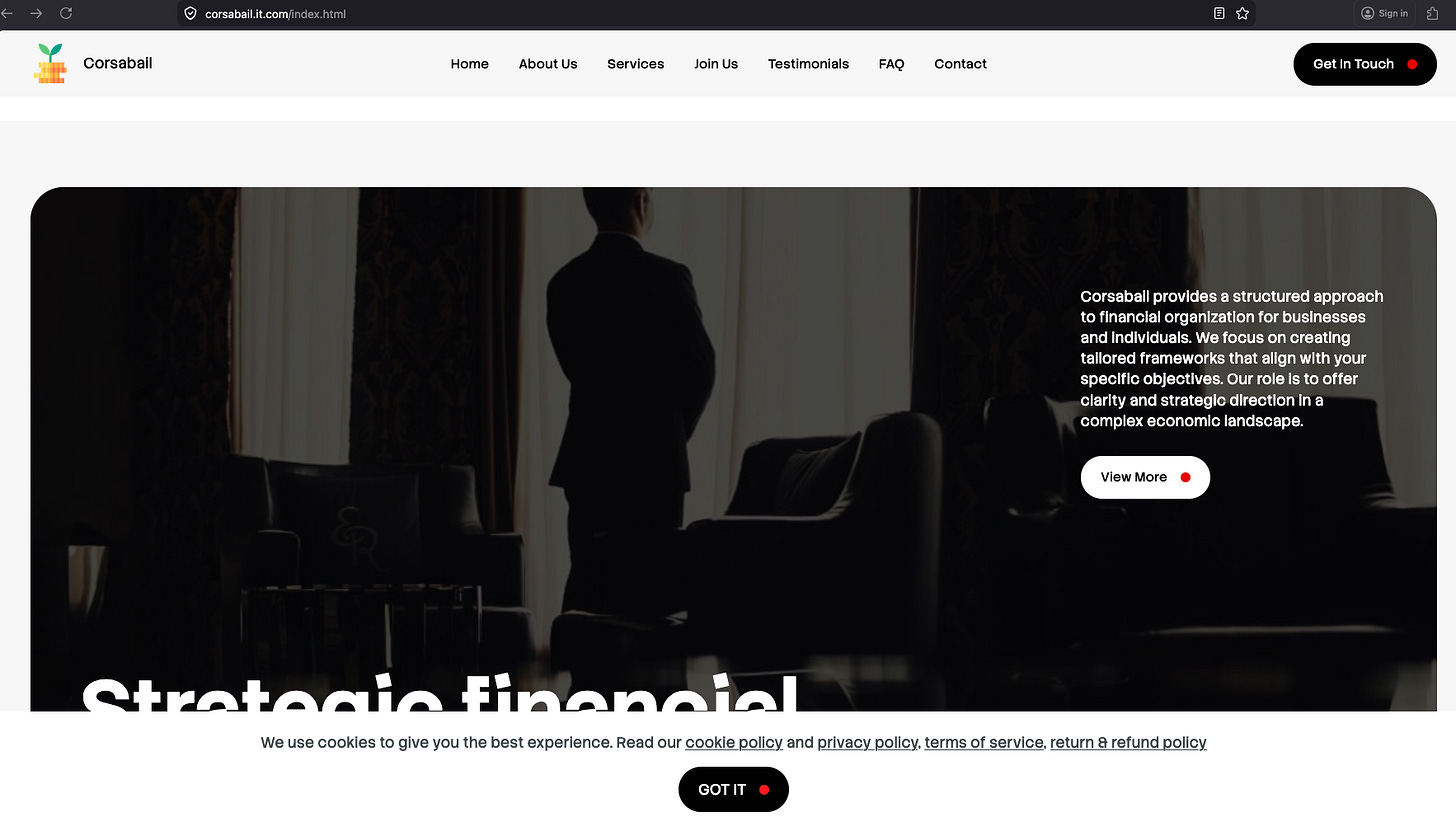
The Cloaking
Untargeted Traffic like traffic originating outside Canada, bots & crawlers, security scanners, policy reviewers—gets routed to the ‘white page’ Corsabail, a generic B2B financial services front with standard cookie consent and privacy policy. Since RBC only operates in Canada, non-Canadian traffic is not in the attacker’s crosshairs.
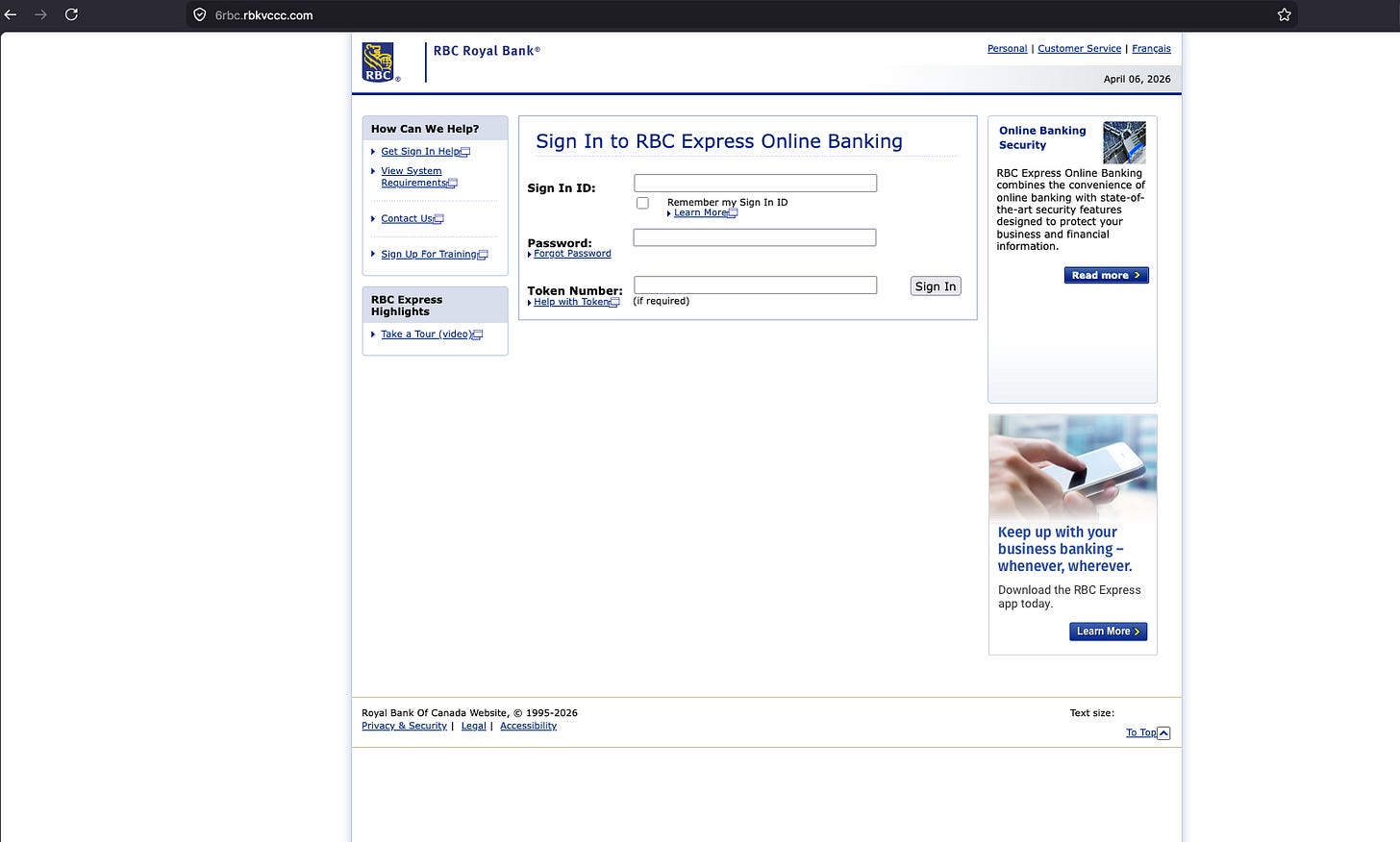
Targeted Traffic Real Canadian users clicking the malicious ad are tracked by a click parameter and get a 302 redirect immediately. The attacker’s server detects the valid ad click and sends the victim to the phishing site at 6rbc.rbkvccc.com:
The money page is a high-quality, well-made clone of the real RBC Express login page. Even the attacker’s subdomain 6rbc is deliberately chosen and designed to impersonate the real, legitimate RBC Express login page, which is https://www6.rbc.com/
What Happens When You Submit Credentials
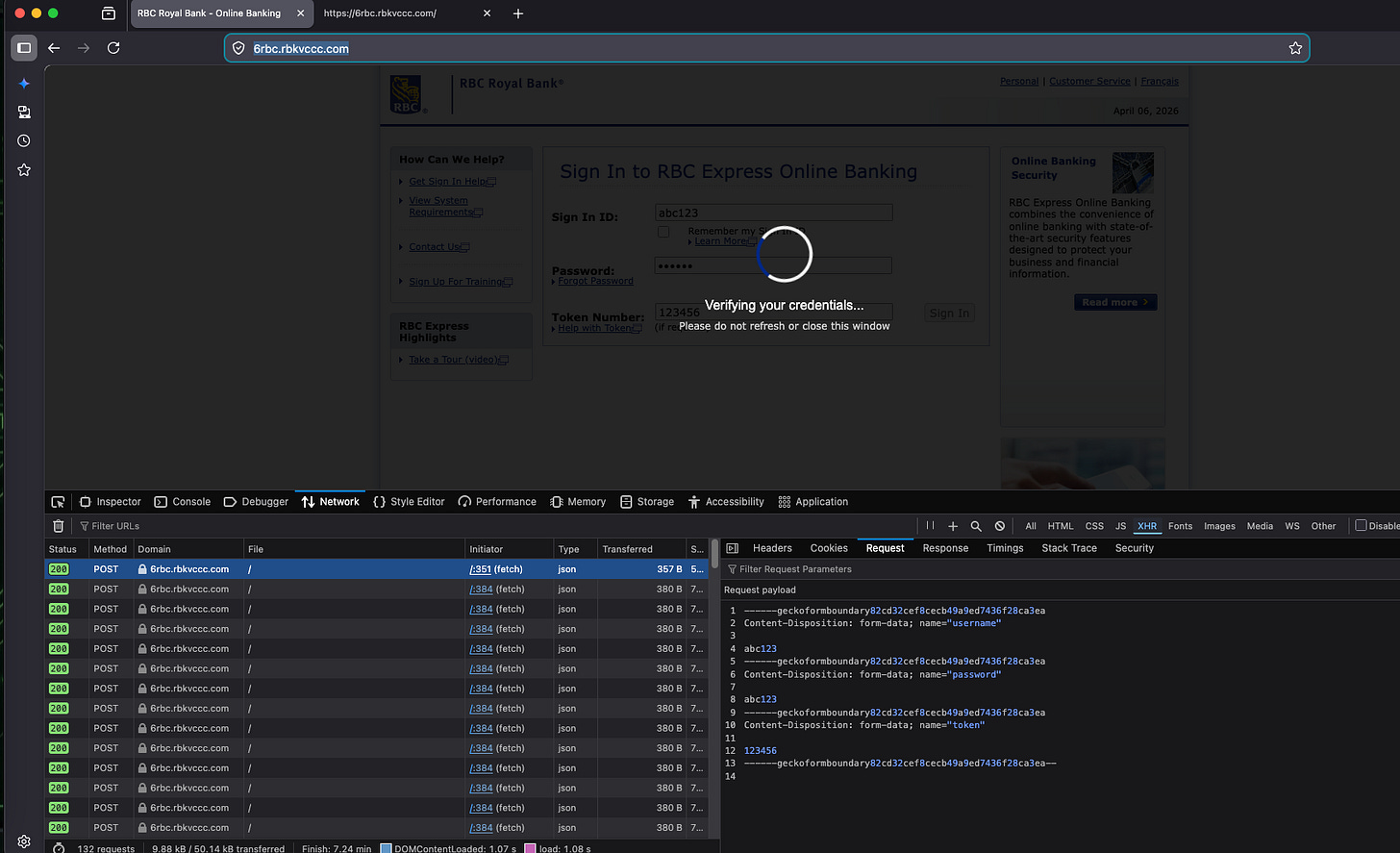
Once you enter your Sign In ID, Password, and hardware Security Token, the real attack begins:
Your credentials are captured and immediately POSTed to the attacker’s server.
A polling loop starts, every 3 seconds asking “did the real bank accept these credentials yet?”
The attacker’s operator attempts your credentials against the real RBC backend.
Two outcomes:
If the bank accepts your login, the attacker relays your session back to you and redirects you to the real
rbc.com. You’re logged in. The attacker is also logged in—but you won’t know it.If the bank rejects your credentials (bad token, expired multi-factor authentication), the fake page surfaces an “Invalid Token” modal asking you to enter a fresh one. The victim re-enters their OTP, thinking they made a mistake. The attacker relays the new OTP to the real bank and tries again.
This entire relay happens in the background. To victims, it feels like a slow login. To RBC’s phishing and fraud team, it looks like a legitimate login attempt clearing multi-factor authentication.
Technical Analysis
Redirect Chain
corsabail.it.com
→ 6rbc.rbkvccc.com/?ref=1ase45df-d234mx8y-sda45cvds-uyj5342m-sd124d2eAiTM Real-Time Credential Relay: On form submission, the phishing kit POSTs harvested credentials to the server (username, password, token) and enters a 3-second polling loop (startPolling()), waiting for the attacker to attempt the credentials against the live RBC backend. The ref UUID functions as a per-session tracking token correlating the ad click to the credential harvest. Each page instance carries the server-injected victimId (e.g., victim_12s7hl6wefd7y54wrb) enabling operator-side session management across concurrent victims.
Live MFA Token Relay: When the server signals status: failed (hardware token rejected or expired at real RBC), the kit surfaces an “⚠️ Invalid Token” modal that prompts the victim for a fresh OTP, which is relayed via a retry_token=1 POST. This defeats hardware multi-factor authentication token MFA without requiring a local proxy.
Closing Remarks
This bank phishing attack combines three techniques that, individually, are well-understood:
Cloaking kits used in malvertising
AiTM credential relay (multi-factor authentication bypass)
Real-time operator-driven exploitation (human-in-the-loop)
What makes it notable is the automation and scale. By using ad tech as a delivery mechanism, the attacker is able to deliver a sophisticated AiTM phishing kit running through programmatic channels to specifically and only target Canadian RBC Express business users at scale, with real-time relay infrastructure and multi-factor authentication token handling built in. The campaign adds to the increased sophistication of the payloads that malvertisers are deploying.
Some malvertising threats like ScamClub and DShortiez operate at huge scale through volume and velocity. They are highly disruptive and rarely go unnoticed. On the other hand, there’s a quieter category worth paying attention to: lower-volume, yet highly malicious campaigns that weaponize ad tech as a distribution vector for advanced payloads like AiTM phishing kits and credential harvesting.
The impact of these payloads is devastating to victims because they suffer immediate financial loss and long-term privacy loss. It is often a long recovery process that can take weeks or months of legal and bureaucratic hurdles to restore credit, identity, and financial security.
IOCs
Ad domain: corsabail.it.com
Phish base domain: rbkvccc.com
Phish URL: https://6rbc.rbkvccc.com/